The term abacus darknet refers to a specific area of the internet known for its anonymity and privacy features, often associated with activities outside the mainstream web. Understanding how this environment operates is crucial for anyone who seeks to navigate the complexities of online safety and security. This article explores the concept of the abacus darknet, the tools and technologies that enable it, and the implications it carries for users.
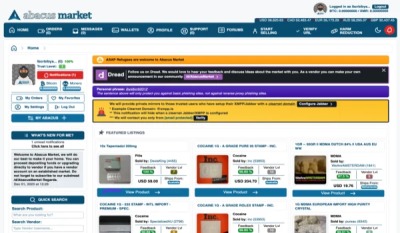
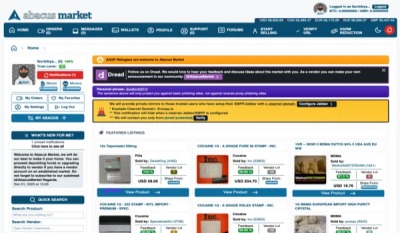
- Abacus Market, one of the largest remaining darknet drug marketplaces catering to Western users, has suddenly disappeared, triggering widespread speculation of a deliberate exit scam.
- In August 2015 it was announced that Interpol now offers a dedicated Dark Web training program featuring technical information on Tor and cybersecurity and simulated darknet market takedowns.
- The marketplace particularly focused on Australian customers while offering a comprehensive range of illicit drugs including stimulants, psychedelics, opioids, and prescription medications.
- STYX Market emerged in 2023 as a specialized dark web marketplace focused on financial fraud and data.
- The dark web market landscape shifts constantly.
- Indeed, they must frequently be accessed by cybersecurity organizations conducting threat hunts or defending their networks or those of their clients.
In April, TheRealDeal, the first open cyber-arms market for software exploits as well as drugs, launched to the interest of computer security experts. However Black Bank, which as of April 2015update captured 5% of the darknet market's listings, announced on May 18, 2015, its closure for "maintenance" before disappearing in a similar scam. By September 2014, Agora was reported to be the largest market, avoiding Operation Onymous; as of April 2015update, Agora has gone on to be the largest overall marketplace, with more listings than the Silk Road at its height.
This makes it difficult for law enforcement agencies like the FBI, CIA, and international partner organizations to disrupt illicit activities. It can simply be a dangerous proposition to peruse the Dark Web and engage with whoever you may meet, especially if it means revealing any personal data. This is where things might get just a bit confusing, as the Dark Web is nearly synonymous with illegal activity.
What is the Abacus Darknet?
The abacus darknet is often linked with underground communication networks that facilitate a range of activities, some of which may be illegal or unethical. Unlike the surface web, which includes all publicly accessible websites, the darknet employs specific software, configurations, or authorization to access. The most common platforms associated with the darknet are Tor and I2P, which allow users to visit sites that are not indexed by traditional search engines.
The Anatomy of the Darknet

At its core, the abacus darknet operates on the principles of anonymity and cryptography. This level of privacy attracts a range of users, from whistleblowers and activists to those engaging in less savory motives. The architecture of the darknet comprises various layers, with sites often ending in a '.onion' domain for Tor or '.i2p' for I2P, making them inaccessible through conventional browsers.
How to Access the Abacus Darknet
Accessing the abacus darknet requires specific software designed to anonymize user data and bypass censorship. The most popular approach involves downloading the Tor Browser, which allows users to connect to the .onion sites. It's essential to approach this with an understanding of the risks involved, as not all activities on the darknet are legal, and some may expose users to malicious software.
Popular Uses of the Abacus Darknet
While the abacus darknet can be associated with illegal activities, it also serves significant purposes. For example:
- Whistleblowing: Individuals can report misconduct without fear of retaliation.
- Privacy-focused communications: Activists and journalists often use it to evade surveillance in oppressive regions.
- Research and information exchange: Academic discussions and research can take place in an environment free from mainstream scrutiny.
The Risks Involved
Navigating the abacus darknet comes with its set of risks. The anonymous nature of this part of the internet makes it a breeding ground for scams and malicious activity. Users may encounter phishing attempts, hackers, and illegal content that can have serious implications, including legal action. Therefore, it is vital for anyone exploring this space to exercise caution and make informed decisions.
Best Practices for Navigating the Abacus Darknet
If one decides to explore the abacus darknet, adhering to certain best practices can enhance safety:
- Use a VPN: A Virtual Private Network can add an extra layer of anonymity.
- Be discreet: Avoid sharing personal information; maintain a low profile.
- Stay informed: Keep abreast of the latest news and developments regarding darknet technologies and threats.
Conclusion
Understanding the abacus darknet is essential for anyone looking to grasp the complexities of online security and privacy. Whether utilized for legitimate purposes or otherwise, knowledge about this hidden aspect of the internet empowers users to make safer and more informed choices. As the landscape of digital communication evolves, staying educated about these technologies can help protect individuals and communities alike.