In the continually evolving landscape of the internet, the darknet presents a unique space for anonymity and privacy. Among the various platforms and services, the abacus darknet url serves a distinct purpose. This article aims to provide clarity on the subject, ensuring that readers understand the significance of the abacus platform within the darknet ecosystem.
- This encourages vendors to provide good service.
- Stealer logs are packages of data stolen by malware from infected computers.
- In a post-mortem report, GMX said the exploit did not affect GMX V2 and outlined steps to disable GLP minting on Arbitrum, reimburse affected users and prevent similar vulnerabilities in GMX forks.
- You’ll also learn how to monitor for your organization’s exposed data.
- This isn’t just a market—it’s a hub where people trade more than goods.
- Brian’s Club was one of the largest carding markets before facing law enforcement pressure.
Established vendors with hundreds of positive reviews can charge premium prices and attract more customers. Without continuous monitoring, security teams are always reacting to breaches that threat actors discovered first. The key differences are the goods being sold, the payment methods accepted, and the infrastructure required to access them. Russian Market acts as a broker, connecting sellers of stolen data to buyers.
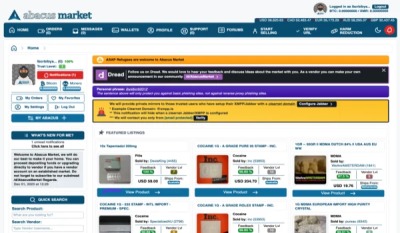
Abacus Darknet Url
The abacus is primarily recognized within the underground communities for facilitating transactions and information sharing while maintaining user anonymity. Below are critical aspects of the abacus platform that every user should be aware of:
Key Features of Abacus Darknet Url
- Privacy Protection: The platform utilizes advanced encryption techniques to safeguard user identities.
- Accessibility: Addresses for the abacus can only be accessed through specific browsers designed for the darknet.
- Diverse Offerings: Users can find a range of services, from marketplaces to forums that discuss various topics.
How to Access the Abacus Darknet Url
- Download and install a suitable darknet browser, such as Tor.
- Ensure your connection is secure and anonymous.
- Input the abacus darknet url into the browser to gain access.
Understanding the Risks
While the darknet offers numerous opportunities, it's vital to recognize the associated risks:

- Security Threats: Users may encounter malware or phishing attempts.
- Legal Considerations: Engaging in illegal activities can lead to severe legal repercussions.
- Scams: Not all services on the darknet are reliable; caution is necessary.
Frequently Asked Questions (FAQs)

Q1: Is the abacus darknet url safe to use?
A1: While the platform prioritizes anonymity, users must remain vigilant about security threats and scams.
Q2: What can I find on the abacus darknet?
A2: The abacus offers a variety of services, from marketplace transactions to forums for discussions on numerous subjects.
Q3: Do I need special software to access the abacus?
A3: Yes, a darknet browser like Tor is essential for accessing the abacus and other darknet platforms securely.
Conclusion
The abacus darknet url represents just one facet of the complex darknet environment, characterized by both opportunities and risks. Understanding how to navigate this space can empower individuals, foster informed decisions, and enhance personal safety while exploring the less visible aspects of the internet. As with any online activity, exercising caution and staying informed are paramount.