Since 0day vulnerabilities are, by definition, unknown until discovered, deploying layered security measures and isolating critical systems can limit damage in case of a breach. Adhering to best practices in security also involves keeping all software and dependencies up to date to patch known vulnerabilities. In fact, we were surprised to find that 0day.today has published more exploits per year than EDB since 2012 (with the exception of 2019). “Completely avoid the scam/scum and enjoy real code, real information and real products.” In 2022, 0day.today published 943 exploits, and EDB only managed 401. A beautiful intermediate-day onion with red skin and crisp white flesh.
Here, users can discuss the latest trends in information security while navigating the complexities of the underground black market. This creates a cycle where hackers are constantly on the lookout for unaddressed flaws within software or systems that they can exploit. When a new vulnerability is discovered, it becomes a potential exploit that can be packaged in various forms, including malware. Not only can the last relay before the onion service not see all of your decrypted network traffic, I don't believe they can tell they are even the last relay. Exploiting such vulnerabilities can lead to significant breaches of user anonymity and system integrity.
The digital landscape is ever-evolving, and with it, new terminologies and concepts emerge that warrant attention. One such term is 0day onion, which intertwines the realms of cybersecurity and the deep web. Understanding this concept is essential for anyone interested in cybersecurity, digital privacy, or simply navigating the online world more safely. This article will delve into what 0day onion signifies, its implications, and the broader context surrounding it.

What is 0day Onion?
The phrase 0day refers to vulnerabilities in software that are unknown to the vendor, meaning there is no immediate fix available. Cybercriminals often exploit these vulnerabilities before they are patched, causing significant harm. On the other hand, the term onion relates to the onion routing technique used in the Tor network, allowing users to access the deep web anonymously. Thus, 0day onion typically refers to previously undisclosed software vulnerabilities that are being discussed or traded on hidden forums within the Tor network.
The Significance of 0day Onion
- Consequently, these platforms have become frontiers for criminal enterprise, raising significant concerns about security, privacy, and law enforcement challenges.
- Navigating these legal landscapes will be crucial for developers aiming to expand the utility and accessibility of onion-based technologies in the future.
- In the context of 0day onion sites, maintaining operational security (OpSec) is paramount.
- It also includes a dark web monitoring feature that crawls the dark web and alerts you if your details show up anywhere.
- Unlike flaws in mainstream software, a Tor-specific exploit is not merely a privacy risk; it is a direct attack on the promise of untraceable communication and censorship circumvention for journalists, activists, and ordinary citizens worldwide.
Understanding 0day onion is crucial for several reasons:
- Cybersecurity Awareness: Knowledge of these vulnerabilities can aid in the development of more robust security measures, as organizations can better prepare against potential threats.
- Digital Hygiene: Users must understand the risks associated with unpatched software and the dark web in general to protect their personal information and data.
- Ethical Hacking: Ethical hackers and security professionals can utilize this knowledge to seek out vulnerabilities before malicious actors can exploit them.
How 0day Onion Operates
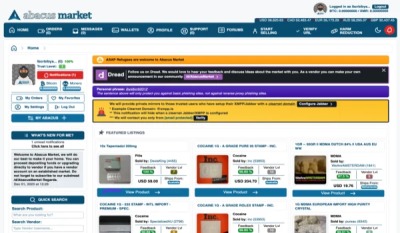
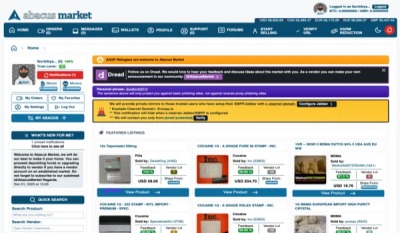
The trading of 0day onion vulnerabilities usually occurs in online forums where anonymity is paramount. These hidden spaces are challenging to access and navigate, often requiring specific tools and knowledge to reach. Here, skilled hackers discuss vulnerabilities, share exploits, and sometimes even sell access to these vulnerabilities to other hackers or interested parties.
Risks and Implications
While the trade of 0day onion vulnerabilities may seem intriguing, it carries significant risks. Exploiting these vulnerabilities can lead to data breaches, financial fraud, and various criminal activities. Additionally, organizations that fall victim to such attacks may face severe reputational damage, legal repercussions, and financial losses. Thus, the 0day onion aspect of cybersecurity is a double-edged sword, showcasing both the ingenuity of hackers and the critical need for vigilance.
Protecting Yourself from 0day Onion Exploits
To safeguard against 0day onion vulnerabilities, consider implementing the following strategies:
- It is a Vulnerability Management solution designed to help security teams with Exploit, Research, Security.
- Zero-day sales have become a lucrative underground trade in recent years, with government intelligence and law enforcement agencies often the highest bidders.
- 0-days are special because your target has no idea such a vulnerability even exists.
- FullHunt is rolling out the complete 0day.today archive, featuring 39,408 exploits and vulnerability research from almost 30 years of security work.
- Regular Updates: Keep your software and systems updated to minimize the risk of being exploited through known vulnerabilities.
- Use Antivirus Software: A good antivirus program can help identify and block threats exploiting unpatched vulnerabilities.
- Education and Awareness: Stay informed about the latest cybersecurity trends, including potential threats associated with 0day onion.
- Strong Passwords: Ensure that you use strong, unique passwords for all your accounts and change them regularly.
Conclusion
The concept of 0day onion serves as a reminder of the complexities and dangers present in the digital world. By understanding these vulnerabilities and their potential consequences, individuals and organizations can better prepare themselves against cyber threats. Awareness, education, and proactive measures are critical in navigating the cybersecurity landscape safely.