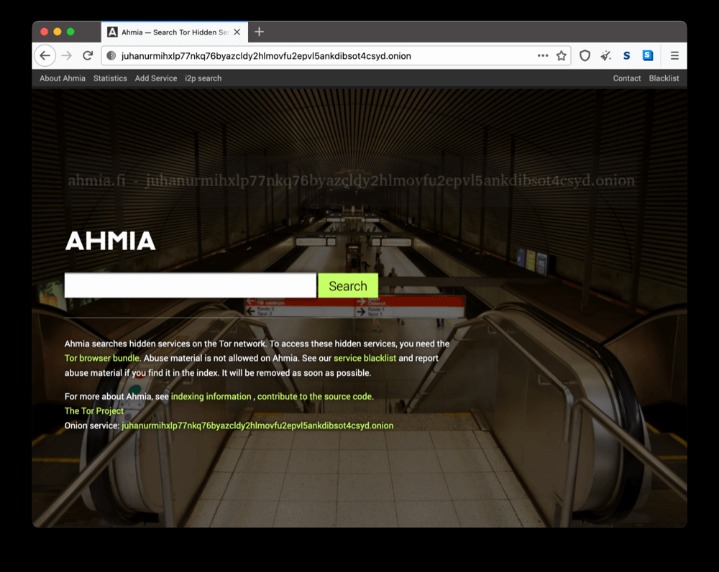
OnionLand is a modern, user-friendly search engine. Also, the simple interface lacks the advanced search options necessary for efficient and targeted searches. The accuracy of its search results is another concern. DeepSearch is an open-source search engine known for its simple interface. It's ideal for teams that value automation and privacy, yet still require visibility into unfiltered networks. This system is designed to blend wide visibility with user-driven filtering, keeping the search results manageable.
The .onion dark web is a term that evokes a mixture of curiosity and caution. Many people have heard of it but are often unaware of what it actually entails and how it operates. This article aims to demystify the .onion dark web, providing insights into its structure, potential uses, and the implications it holds for online safety. Understanding this hidden part of the internet can empower individuals to navigate it with awareness and informed choice, significantly enhancing their online security.
Tor is a powerful tool for those seeking privacy and access to uncensored information. Donations from organizations like Mozilla and Electronic Frontier Foundation help fund the development of privacy tools and keep Tor accessible. Advanced de-anonymization techniques, such as traffic analysis, pose a challenge for Tor.
.onion Dark Web
The .onion dark web refers to content that is accessible only through specific software, primarily the Tor browser. This section of the internet is not indexed by traditional search engines and is known for its anonymity and privacy features. While the dark web often carries a negative connotation due to associations with illegal activities, it is crucial to recognize that it serves various purposes, including those that promote freedom of speech, privacy, and protection for whistleblowers and activists.
- If you want to access the dark web through Tor, it’s best to start by learning some cybersecurity best practices.
- The dark web is intentionally hidden and requires specialized software, such as the Tor browser, to be accessed.
- These sites were replaced by new darknet marketplaces.
- Tor has around 2 million daily users exploring over 65,000 onion sites.
- The traffic is routed via the closest nodes in the open net to create efficient routing.
How the .onion Dark Web Works
- As Tor is encrypted by default, most dark web websites don’t use this same certification.
- That even if you set loose a search engine to war-dial the entire address book of Tor/Onion V2 and V3 addressing.
- It's ideal for teams that value automation and privacy, yet still require visibility into unfiltered networks.
- Even without considering the content of the sites, these factors give the entire network of onion sites a sense of untrustworthiness.
- One other thing makes darknets different from the broader internet and other overlay networks.
To access the .onion dark web, users must first download the Tor browser, a unique web browser designed to facilitate anonymous communication. The Tor network obscures users' locations and usage from anyone performing network surveillance or traffic analysis, which is why it is often used by individuals requiring protection from governmental or organizational scrutiny.
Websites on the .onion dark web typically have addresses ending in “.onion,” which are not recognized by standard browsers. This architecture allows for a host of activities that range from the illegal to the benign. Accessing these sites often requires specific knowledge or links, making it less approachable than the surface web.
Uses of the .onion Dark Web
The .onion dark web hosts a variety of content, including:
- Whistleblowing platforms: Secure spaces for individuals to report misconduct without fear of reprisal.
- Forums and communities: Spaces where users can discuss sensitive topics anonymously, often related to activism or privacy rights.
- Privacy-oriented services: Tools and services that cater to individuals seeking to maintain their anonymity online.
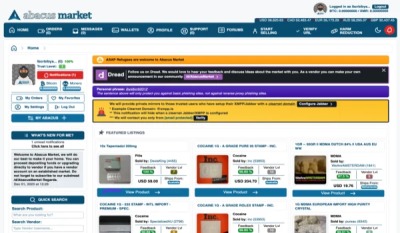
- Marketplaces: While some facilitate illegal goods and services, others may offer legal goods with a focus on privacy.
The Risks Involved
Engaging with the .onion dark web carries inherent risks. Many sites might expose users to illegal content, scams, or malicious software. Moreover, law enforcement agencies monitor dark web activities closely. Users must exercise extreme caution, remain informed about the legal implications of their actions, and consider using robust cybersecurity practices.
Safeguarding Yourself While Exploring
For those who choose to explore the .onion dark web, the following safety tips can help mitigate risks:
- Use a Virtual Private Network (VPN): Enhances your anonymity and adds an extra layer of security.
- Keep software updated: Regular updates can protect against vulnerabilities.
- Be cautious with personal information: Avoid sharing any identifying details.
- Beware of scams: Always verify the legitimacy of any services or sellers before making transactions.
Conclusion
The .onion dark web is a complex and multifaceted space that is often misunderstood. By educating themselves about its functionalities, potential benefits, and associated risks, individuals can make better decisions about their online activities. Knowledge is a powerful tool for protection and empowerment in the ever-evolving landscape of digital privacy and security.